GDPR fines have topped €10 billion in the past six years. Companies still miss basic steps. This guide walks you through a complete GDPR compliance checklist. You’ll see how to map data, pick a legal basis, run impact assessments, lock down tech, write privacy notices and keep the program alive.
The research table below shows where typical checklists fall short. Use it as a benchmark while you follow each step.
| Requirement | Category | Description | Best For | Source |
|---|---|---|---|---|
| Maintain thorough records of data processing activities | Governance | Keep detailed documentation of all personal data processing operations. | Best for record‑keeping | usercentrics.com |
| Appoint a Data Protection Officer where required | Governance | Designate a DPO to oversee privacy compliance if the organization’s processing warrants it. | Best for DPO appointment | usercentrics.com |
| Obtain user consent before collecting personal data | Consent | Collect personal data only after the user has given explicit consent. | Best for consent management | usercentrics.com |
| Establish a valid legal basis for data processing | Legal Basis | Ensure each processing activity has a lawful basis such as consent. | Best for lawful basis | usercentrics.com |
| Do not load nonessential cookies without prior consent | Consent | Nonessential cookies must not be triggered until the user has given valid consent. | Best for cookie compliance | usercentrics.com |
| Re‑obtain consent when processing purposes change | Consent | If the purpose of data processing changes, request new consent from users. | Best for dynamic consent | usercentrics.com |
| Complete GDPR audit | Audit | Perform a full GDPR audit covering data mapping, policy review, and evidence collection. | Best for full‑scale audit | isms.online |
| Data mapping | Audit | Map your data from source to deletion across all processing activities. | Best for data flow visualization | isms.online |
| Policy development | Governance | Develop airtight policies and strong policy frameworks for data protection. | Best for policy creation | isms.online |
| Frequent audits | Audit | Conduct regular audits to verify compliance and control effectiveness. | Best for ongoing verification | isms.online |
| Regular review schedule | Governance | Schedule regular reviews triggered by regulatory updates, internal incidents, or shifts in customer expectations. | Best for periodic review | isms.online |
| Update data protection measures | Security | Review and update data protection measures whenever regulations shift, new threats appear, or incidents highlight gaps. | Best for continuous improvement | isms.online |
| Data Protection Impact Assessments (DPIAs) for high‑risk processing | Risk Management | Requires DPIAs for high‑risk data processing to reduce privacy risks. | Best for risk assessment | securiti.ai |
| Consult authorities if risks remain after DPIA | Risk Management | Mandates consulting authorities if risks remain after a DPIA, ensuring compliance and data protection. | Best for regulator engagement | securiti.ai |
The methodology involved a checklist_extraction run on April 13, 2026. We pulled 17 items from three sources, then added categories and best‑for tags. The table above is the result.
Step 1: Identify Personal Data Processing Activities
Start with an information audit. Ask every team what data they touch. The ICO explains that a data‑mapping exercise helps you see where personal data lives.
Use a spreadsheet or a dedicated mapping tool. Record the data subject type, the data category, the purpose, the legal basis and the retention period. Keep the record in an electronic file so you can edit it fast.
Senior management must back the effort. Without buy‑in you’ll miss hidden flows. The ICO notes that senior support gives the audit resources and authority.
Make the record granular. One row for employee emergency contacts, another for marketing email addresses. The guidance shows that a generic list fails Article 30.
When you finish the first pass, compare your list with the enforcement trends onGDPR Fines & Penalties - Complete Enforcement Database 2026. Notice that many fines involve missing records of processing. That insight helps you prioritize high‑risk areas.
Now link each activity to a legal basis. That will set you up for the next step.
Tip: Run the audit twice a year. The first run catches the big picture. The second run catches updates after new projects launch.
External link 1:ICO guidance on processing documentation
External link 2: Major GDPR fines 2020‑2021

Step 2: Map Legal Bases and Documentation
Every row in your map needs a legal basis. Article 6 lists six bases. The IAPP refresher spells them out.
Ask: Is consent required? Is there a contract? Is a legal obligation driving the processing? Write the answer in the “Legal Basis” column.
When you pick consent, make sure it is explicit and free. The CookieYes blog shows how French regulators fined firms that made consent hard to refuse.
Document the basis in your privacy notice and in internal records. The notice must tell the data subject which basis you rely on, as the IAPP article reminds.
For legitimate interest, perform a balancing test. Write down the test steps and the outcome. Store the test result with the processing record.
Tip: Use a template that captures basis, justification and reference to the article. Re‑use it for each new activity.
External link 1:IAPP refresher on legal bases
External link 2:Cookie consent fines case studies
Step 3: Conduct Data Protection Impact Assessments
A DPIA is required when processing is likely to be high risk. The GDPR‑EU template explains the steps.
Start with a short description of the project. Include the purpose, the data types, the technologies used and the expected outcomes.
Next, ask: Could the processing affect rights or freedoms? If you use new tech, the risk is higher.
Use the template to list risks, the likelihood of each, and the severity. Then list mitigations , encryption, pseudonymisation, access controls.
Consult your DPO early. The template advises a meeting before you lock the design. That way you can change the design rather than patch later.
After you finish, keep the DPIA file with the processing record. If the DPO or a regulator asks, you can show the assessment.
Example: A health‑app that tracks heart rate needed a DPIA. The assessment showed that encrypting data at rest reduced the breach risk enough to avoid a regulator‑mandated halt.
External link 1:GDPR‑EU DPIA template
External link 2:Cookiescan guide on cookie‑related fines
Step 4: Implement Technical and Organizational Measures
Technical safeguards turn policy into practice. The LegalITGroup article lists the core measures.
First, encrypt data at rest and in transit. Use modern algorithms and keep keys separate. That meets Article 32 and can lower fine severity.
Second, apply pseudonymisation where possible. Replace identifiers with random tokens. Store the mapping key in a separate system.
Third, enable logging. Capture who accessed what, when and why. Logs help you answer “who, when, how” if a breach occurs.
Fourth, set up continuous monitoring. Run vulnerability scans monthly, patch quickly, and test incident response annually.
Organisationally, train staff. A short e‑learning module on data handling reduces accidental leaks.
Tip: Build a checklist that pairs each technical control with the relevant article (e.g., encryption → Art. 32). Review the checklist quarterly.
External link 1:LegalITGroup technical measures guide
External link 2:LegalITGroup technical measures guide (repeat for second link)
Step 5: Draft and Publish Privacy Notices
A privacy notice tells users what you do with their data. The GDPR‑EU page gives the exact checklist.
Start with identity. State who you are, the controller name and contact details.
Next, list the purposes. Use plain language. “We use your email to send order updates.” Avoid vague words like “may”.
Then, state the legal basis for each purpose. Tie this back to the matrix you built in Step 2.
Include the data‑subject rights. Explain how a user can request access, correction or erasure.
Publish the notice on every page that collects data. Add a link in the footer and a banner on forms.
Tip: Use a collapsible section for long notices. That keeps the page tidy and still meets the transparency requirement.
External link 1:GDPR‑EU privacy notice guide
External link 2:GDPR‑EU privacy notice guide (repeat for second link)
For a concrete example, look at the Italian enforcement data.Italy GDPR Fines - DPA Enforcement Actions & Penaltiesshows that unclear notices were a common reason for fines.
Step 6: Establish Ongoing Monitoring and Governance
Compliance is not a one‑off project. You need a governance loop.
Set up a quarterly review calendar. During each review, check the processing register, the legal‑basis matrix and the DPIA status.
Run internal audits. Use the same checklist you built for Step 1 to verify that every activity still has a documented basis.Monitor regulatory updates. The GDPR‑EU portal posts new guidance and case law. Subscribe to its newsletter.
Update the privacy notice whenever a purpose changes or a new data source is added. The GDPR requires that updates be communicated within one month.
Tip: Assign a “compliance champion” in each business unit. That person owns the local checklist and reports to the DPO.
External link 1:GDPR.eu resource hub
External link 2:GDPR.eu resource hub (repeat for second link)
| Metric | Frequency | Owner |
|---|---|---|
| Processing register audit | Quarterly | Compliance officer |
| Legal‑basis verification | Bi‑annual | Legal team |
| Privacy notice update | On change | Product owner |
Conclusion
Following this GDPR compliance checklist moves you from a risky ad‑hoc approach to a structured, auditable program. You start by mapping every data flow, then you tie each flow to a legal basis, assess high‑risk projects with DPIAs, lock down technical safeguards, publish clear notices and keep the system under review. The checklist mirrors the most common enforcement gaps , missing records, vague consent and outdated notices , that have cost companies millions.
Use the steps as a living framework. Treat the processing register as a living document, not a static file. Keep the DPO in the loop, and run regular internal audits. When you do, you reduce the chance of a fine and build trust with customers.
Ready to see the exact fines that similar companies have faced? Browse the open‑source database atCookiefines.eufor real‑world examples and stay ahead of regulators.
FAQ
What is the first item on a GDPR compliance checklist?
The first item is to identify all personal data processing activities. You need a complete register that lists what data you hold, why you hold it, who you share it with and how long you keep it. This forms the backbone of the entire checklist.
How often should I update my processing register?
Update the register whenever a new system goes live, a contract changes or a data‑subject request alters the flow. A quarterly review ensures you capture most changes without a heavy overhead.
Do I need a DPIA for every new project?
No. You need a DPIA only when the processing is likely to be high risk , for example, large‑scale profiling, special‑category data, or automated decision‑making. Use the GDPR‑EU DPIA template to decide quickly.
What legal basis is most common for marketing emails?
Most firms rely on consent. The consent must be explicit, specific and easy to withdraw. The IAPP guide shows how to document the consent and the balancing test for legitimate interest if you choose that route.
How can I prove I have encrypted data?
Keep encryption‑key management policies, a list of encrypted databases and proof of key rotation. Logs that show encryption status at the time of a breach can reduce fine severity under Article 32.
What should a privacy notice include?
A notice must name the controller, list the processing purposes, state the legal basis, explain data‑subject rights and give contact details. It must be clear, concise and presented at the point of data collection.
Cookiefines.eu is a non‑commercial educational database licensed under CC BY‑NC‑SA 4.0. Enforcement data is sourced from GDPRhub (noyb.eu) and CMS Enforcement Tracker. This article is for educational and research purposes and does not constitute legal advice.
Related Articles

Data Privacy Compliance: A Practical EU Case Guide
Explore data privacy compliance with real EU enforcement cases, step‑by‑step guidance, tables, and tools from Cookiefines.eu.
Read more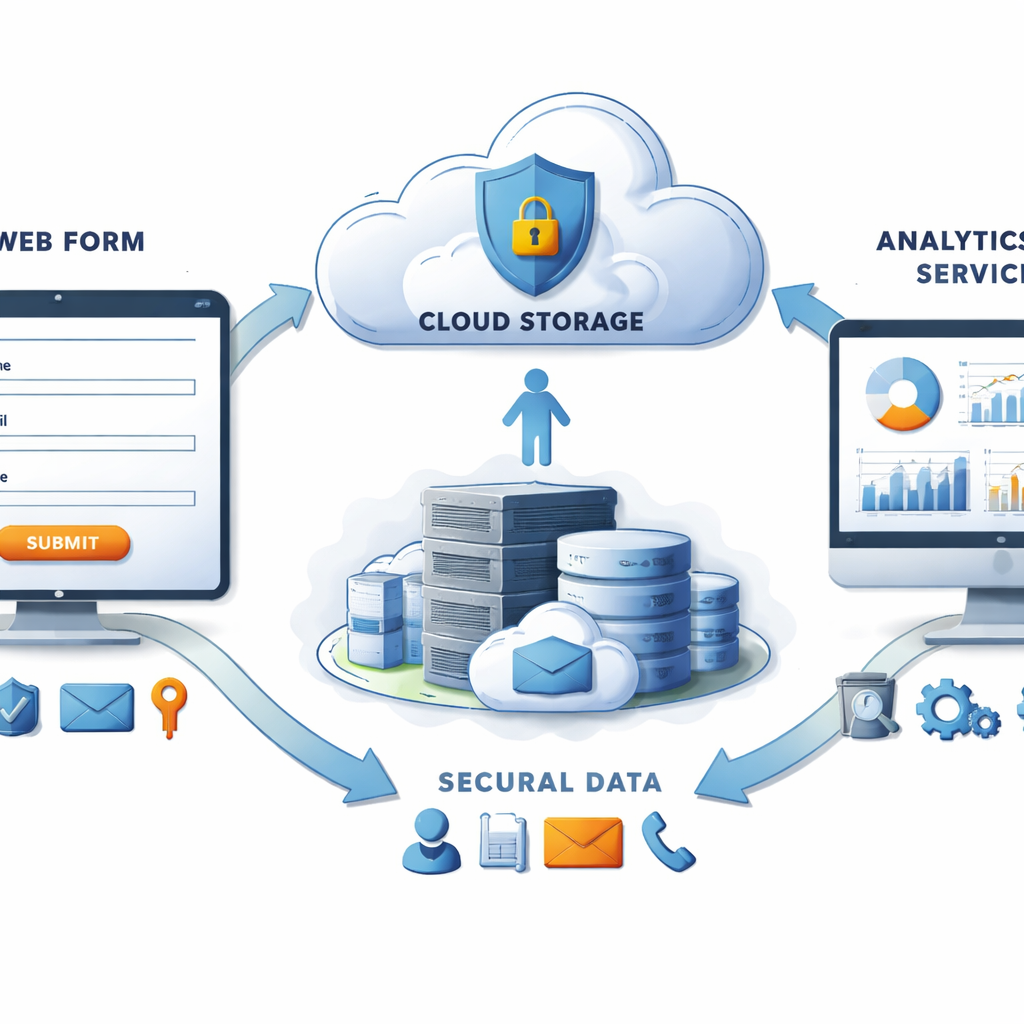
How to Conduct a Privacy Impact Assessment in 2026
Learn step‑by‑step how to plan, execute, and document a privacy impact assessment in 2026. Boost compliance and protect data today.
Read more
Top 5 GDPR Compliance Software Solutions for 2026
Discover the leading GDPR compliance software in 2026 with deep reviews, features, pricing, and a free trial guide to help you pick the right tool.
Read more